This week in web security, we look at what’s next after GDPR, analyze a DDoS attack and release our top blocks of the week.
After GDPR, what’s next for privacy in Canada – circle November 1st
On the heels of GDPR going into full force, we still await PIPEDA changes coming in November that will put Canadian organizations in the hot seat for reporting breaches to users within a very short time-frame. Considering that the recent attention that CIBC’s Simplii and BMO got for a data breach we expect that these changes are going to give us almost daily headlines. It will be very interesting to see what data consent means in Canada since we have taken a pretty high road with CASL as it relates to electronic communications.
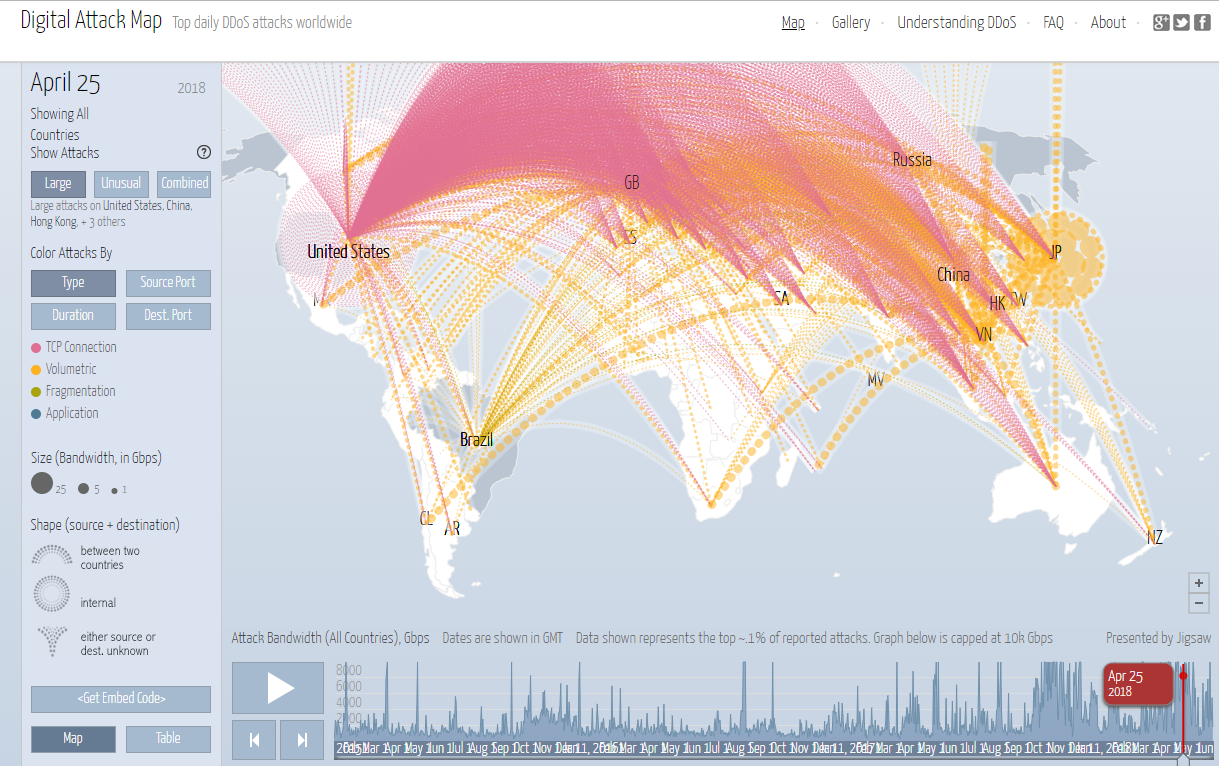
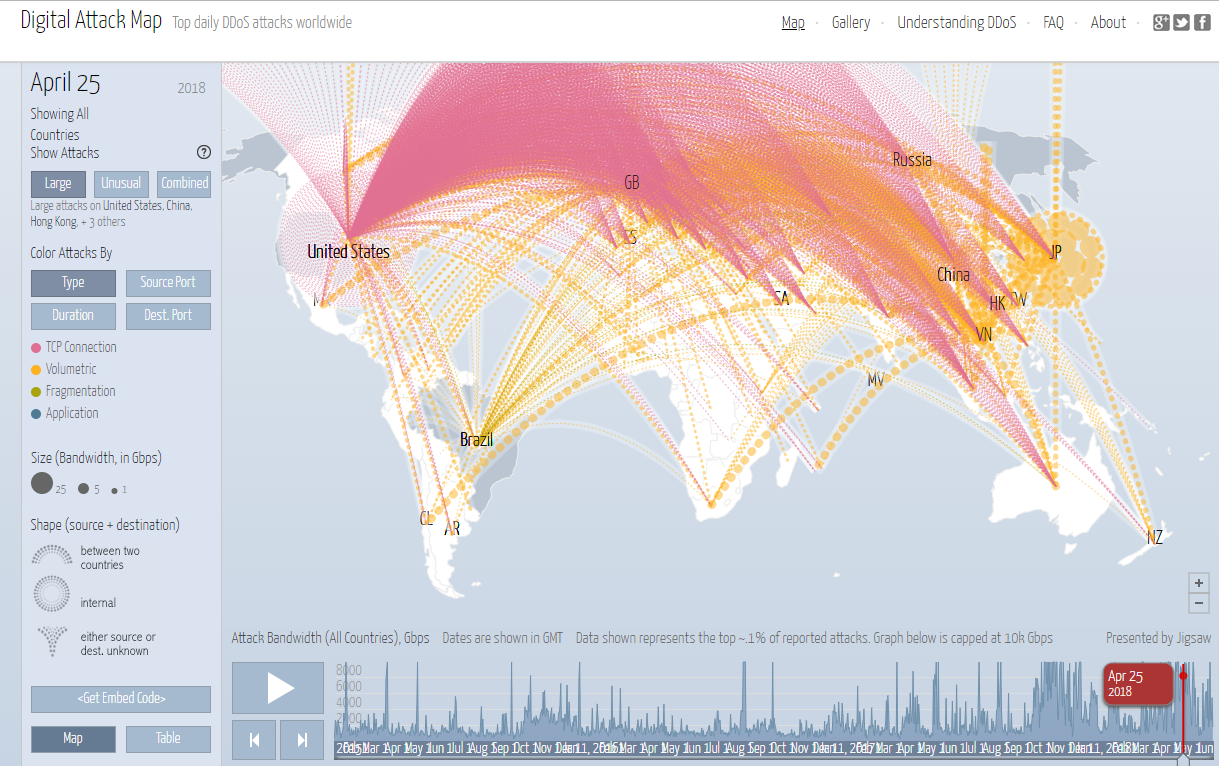
Anything new with DDoS?
It has been just over 1 month since Webstressor was taken offline by authorities. For those who don’t know, this was a tool that could be used to stress-test applications but the reality is that it was also frequently used to launch DDoS attacks. For fun, we looked at the Arbor digital attack map on the day it was shut down to see if there was an impact in their reporting (there wasn’t). While this isn’t quantitative, you don’t see a big change in activity over the days following the 25th of April (shown with the red thought bubble in the image below). The world seems to stay at sustained highs on the map – at least as it pertains to Arbors network.
Have you updated your router yet?
The FBI saw fit to issue a release asking people to update their routers home routers and NAS devices to protect from VPNFilter malware. It was originally reported to be affecting at least 500,000 devices and that number has since been expanded when CISCO announced that it is impacting a broader range of devices. If you know this already then you probably know what to do to protect yourself and do your responsibility to protect the Internet (yes you do have some).
If you don’t, or you ignored the message because…well, FBI, then make sure you update the default passwords and update the firmware regularity. Although routers can be intimidating, you must take the time to understand how to use it. Let’s be honest, you know how to use your kitchen stove and can figure out how to reprogram it’s clock after a power outage and you probably cook way less than you use the internet.
For the majority of people who didn’t know they could type 192.168.x.x into their browser (the “x” is often either a 0 or 1 depending on the router) – please remember to keep your manuals because it is explained there. Alternatively, for visual learners, YouTube is here to help, and here is one of this author’s favorite tech youtubers from linustechtips giving you some other beneficial advice while you are in the router interface doing your update – so it is doubly worth it!
And finally, lets look at our top 10 blocks of the week.
.RU domains continue to grow in frequency with four of the top 10 blocked domains of the week. Bringing up the rear are randomized domains built off .com auto-generated by the malware for command and control. And finally, one that calls it like it is by self-identifying as a hacker and using an anonymizer – thanks for that.
|
Domain |
|---|
|
superyou.zapto.org |
|
dj1.jfrmt.net |
|
76236osm1.ru |
|
soplifan.ru |
|
diplicano.ru |
|
bestonlineserial.ru |
|
dzhacker15.no-ip.org |
|
rvbwtbeitwjeitv.com |
|
erwbtkidthetcwerc.com |
|
rterybrstutnrsbberve.com |
Rob a acquis plus de 20 ans d’expérience de la rédaction, de la présentation et du blogage à l’intention de l’industrie des technologies. Il aborde des thèmes aussi variés que les outils de développement de logiciels, l’ingénierie inverse de Silicon, la cybersécurité et le DNS. De fait, Rob est un spécialiste du marketing passionné qui s’adresse aux professionnelles et aux professionnels des TI en leur donnant les renseignements et les précisions dont ils ont besoin pour s’acquitter de leurs tâches.