Train your team to be your human firewall
The human cybersecurity layer is often the most vulnerable. Learn how we can turn your people into your greatest security assets.
Not all security awareness training programs are created equal.
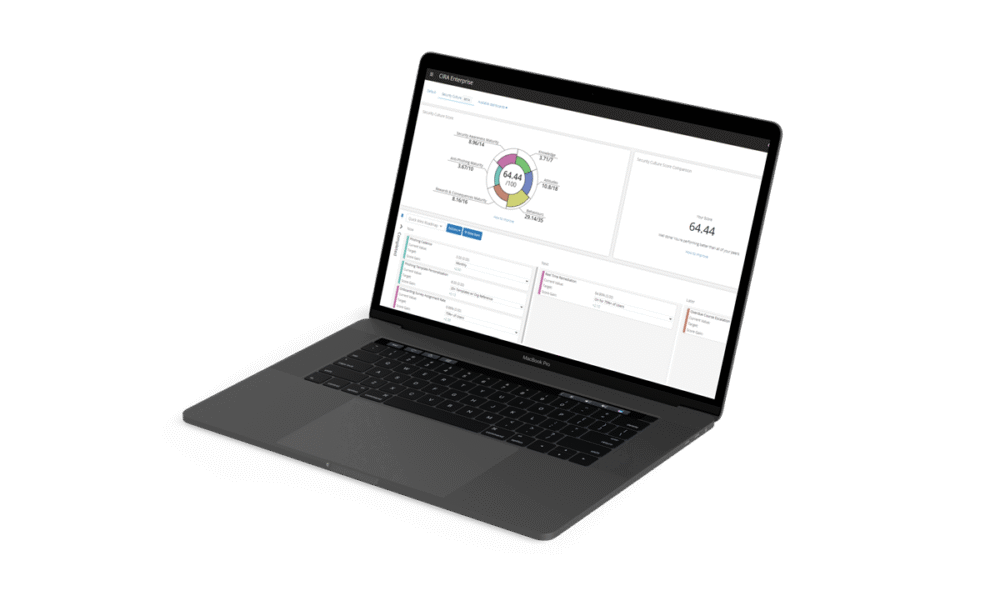
An all-in-one human cybersecurity platform.
Training
Deliver engaging and relevant content to your people about the most important topics, at the right time.
Simulation
Test your team’s ability to recognize and report human engineering attacks with our best-in-class phishing engine.
Reporting
Quickly generate the reports you need for identifying repeat clickers, executive reporting and compliance purposes.
What is cybersecurity awareness training (CAT)?
Cybersecurity awareness training teaches people and companies how to recognize and prevent cyber attacks, reducing the likelihood and impact of a cyber incident.
Our training program, CAT is a platform designed to educate employees on how to protect their organization’s digital assets, data and financial resources. The program combines relevant courses, realistic phishing simulations, robust reporting and risk assessment tools on a dynamic platform built to keep your people engaged and learning.
More features, less setup
-
Launch your training program in an afternoon
Leverage our pre-configured workflows, surveys and curriculums to launch your training program quickly and easily.
-
Assign a wide variety of training materials
Take advantage of our library of bilingual training materials including interactive courses, phishing simulations, workflows, curriculums and print materials to suit every learning style.
With Active Directory and SSO, user management is a breeze. Easily import and remove users and departments. Plus, user sign in has never been easier.
-
Customize training content
Easily customize training content for your organization’s specific needs without any code. Add your brand and colours to dashboards, upload your own courses and more.
-
Detailed reporting
Slice-and-dice training and phishing data to identify repeat clickers, high performing employees and more.
Get your staff started with training today

CIRA partnership at a glance
“We have established a close, collaborative relationship with the CIRA team. This partnership extends well beyond the product itself.”
Anju Sohal,
Senior Program Manager
Partnership since: 2024
ORION Community users: 50,000

Reinvesting into our internet ecosystem